The explosion in the use of Generative Artificial Intelligence in the professional world presents an opportunity to increase productivity on tasks considered time-consuming, while at the same time opening up new possibilities for cybercriminals. Tools such as ChatGPT, the best known in Europe, are constantly evolving and are now capable of producing identical copies of sensitive documents such as invoices, contracts, identity documents, etc. These digital documents are commonly used to deceive recipients and blackmail them emotionally and financially—a practice knownas "phishing ."
As AI learns, the risks of identical reproduction of sensitive documents and data are likely to skyrocket. This threat should not be taken lightly. Fortunately, companies wishing to protect themselves against these risks have the technological means to safeguard the integrity of documents considered strategic.
Better still, by adopting a digitization solution that validates the legal compliance of a paper document converted to electronic format, they accelerate their digitization process and archive their sensitive documents in accordance with best practices using an electronic archiving system (EAS).
AI facilitates scams through social engineering
The ease with which AI can produce deceptively authentic documents is a boon for fraudsters. They now use tools such as language models to create invoices, contracts, or even personalized and accurate tax documents. This makes identifying fake documents more complex, especially since minor errors that were once telltale signs can now be corrected by these technologies.
In the past, complex scams required extensive technical expertise to orchestrate. Today, with user-friendly AI tools, even individuals with basic computer skills can create malware or deceptive chatbots. This democratization of cybercrime amplifies the risk of attacks for all organizations.
Identity documents and ultra-realistic forgeries
AI also makes it possible to create images, videos, and sounds of convincing quality. Soon, it will be possible to produce ultra-realistic identity documents, complete with seals and other official signs of authentication. This naturally brings to mind passports and all the documents required by a third party to certify one's identity.
These advances increase the risk of identity theft, radically transforming authenticity verification strategies. Faced with these risks, companies can respond by implementing a robust strategy to protect their most sensitive documents.
Reliable copying: ensuring document integrity
To protect the integrity of their documents and prevent any attempts at identical reproduction, economic actors can adopt a solution known as reliable copying. What does this involve?
A reliable copy, unlike a faithful copy, takes into account the document's durability and legal compliance parameters. It can therefore replace the original paper document, providing an opportunity for companies to eliminate the need to store original paper documents and take a further step towards digitization. Above all, since Decree No. 2016-1673 of December 5, 2016, a digital copy of a paper document is presumed to be reliable, provided that all appropriate means are used for its creation and storage.
→ Articles 2 and 3 of Decree No. 2016-1673 of December 5, 2016, precisely define the points to be observed in order to validate the compliance of the dematerialization process: electronic fingerprint, qualified time stamp, qualified electronic seal, qualified electronic signature. This also includes storing documents in conditions that prevent any alteration to their form or content.
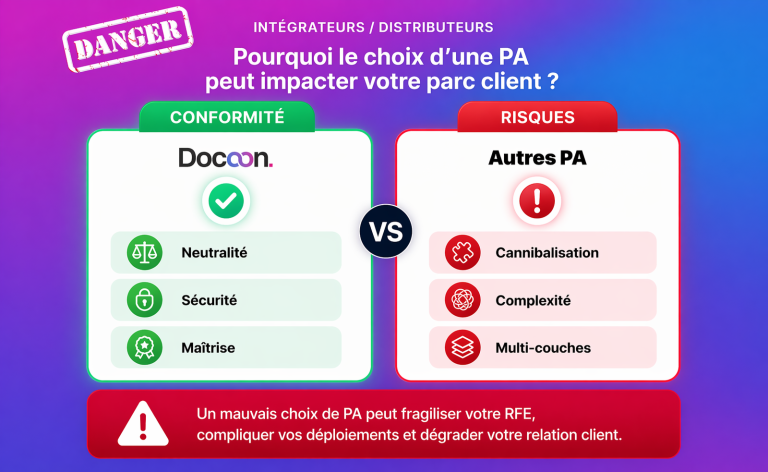
Docoon, France's leading publisher in the development of trusted digital services, offers companies a reliable copying solution that is recognized for its legal compliance (integrity and durability), as it validates all the compliance points set out in the decree of December 5, 2016. Docoon enables companies to digitize all their administrative and confidential documents related to their business (contracts, memoranda of understanding, invoices, pay slips, credit and debit account statements, minutes of meetings and board meetings, etc.) to guarantee their authenticity and integrity.
👉 A reliable copy allows for the reversal of the burden of proof in the event of a dispute over a document, if it is produced in accordance with Decree No. 2016-1673 of December 5, 2016.
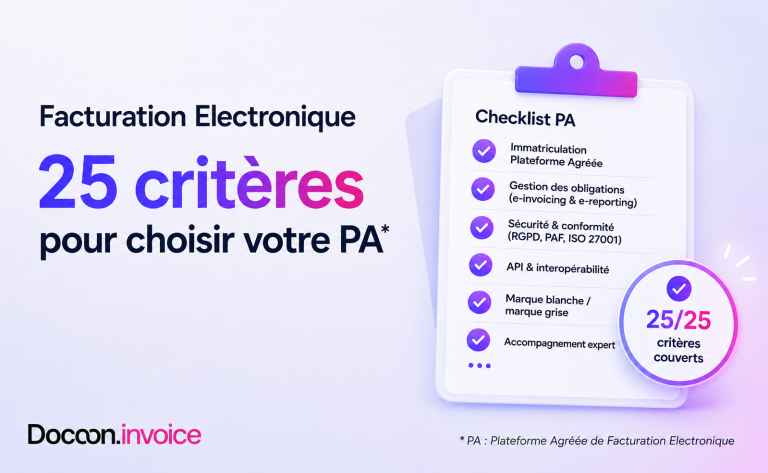
→ Docoon uses reliable copying for electronic invoices. Our solution for the fiscal dematerialization of invoices sales invoices includes an eIDAS signature at the RGS **(2 stars) level.
Choose an NF 461-certified electronic archiving system
In the age of generative AI, protecting documents against potential falsification has become a necessity, but what happens next? Documents must be stored over time with the same requirements: guaranteeing their integrity and more. This is the level of service offered by Docoon with electronic archiving that complies with the Z42-013 standard and is NF 461 certified.
Assigned to the SAE and not to the service provider, NF 461 is the only certification guaranteeing that a tool complies with the rules that ensure the fidelity, integrity, durability, and traceability of digitally hosted documents over the long term. In the event of a dispute, electronically stored documents can then be accepted as evidence.
It is essential for any business to recognize the crucial importance of protecting its sensitive documents from falsification. With the advent of artificial intelligence tools, manipulated and reproduced documents are becoming increasingly sophisticated. It is no longer just a matter of preventing fraud; it is about defending the very integrity of information and the reputation of the company. In the digital age, equipping yourself with the best tools to prevent document falsification or identity theft is no longer a luxury, but a necessity. Be careful when choosing reliable copying solutions, and your company will reap the benefits far beyond simple regulatory compliance!
→ Discover Docoon.Sign, Docoon's electronic signature solution that guarantees document integrity, authenticates the author, and provides proof of consent if necessary.
(1) Phishing is a fraudulent technique designed to trick internet users into providing personal data (account logins, passwords, etc.) and/or banking details by posing as a trusted third party.